Blog
-
UK’s transplant system was world-leading – now it lags behind other Western nations
The UK has failed to keep pace with the rest of the world. Can it regain its status, and how? -
Cuba’s mothers-to-be prepare to give birth in a country plunged into darkness
Two pregnant women tell the BBC’s Will Grant of their hopes and fears as their nation is mired in crisis. -
Signal Phishing Attack: Digital Evidence Points to Russia
For weeks, a wave of attacks has been targeting Signal users in Germany and abroad. Among those targeted are security officials, politicians, and journalists. A CORRECTIV investigation found digital evidence pointing to Russian involvement in the campaign – and a connection to previous attacks in Ukraine and Moldova. -
Inside the Aluminum Supply Chain Linking Irish Industry to Russian Rockets
Along a rugged, wind-swept shore in western Ireland stands Aughinish Alumina, the hulking industrial complex that is Europe’s largest alumina refinery.
Inside the sprawling plant, heat and pressure are harnessed to transform bauxite — a reddish rock mined oceans away — into alumina, the main raw material needed to produce aluminum.
Strong and resistant to corrosion, aluminum is vital for manufacturing military hardware like missiles, drones, and aircraft. That’s one reason why the European Commission has called on member states to stockpile alumina as a defense against hostile powers.
Yet rather than remaining in the European Union, the majority of the Aughinish factory’s exports are shipped to Russia’s largest aluminum smelters. Those smelters, in turn, feed into a supply chain of sanctioned defense contractors whose weapons have killed thousands of civilians in Ukraine, a new investigation by OCCRP and partners has found.
Credit: Alan Betson/The Irish Times
View of the Aughinish Alumina refinery in Country Limerick, Ireland.
Reporters could not track the final destination of a specific batch of Aughinish’s alumina, as the powdery substance is typically mixed together with alumina from other sources in the smelting process.
However, customs and trade data show that since 2023, more than half the Ireland-based refinery’s alumina exports have gone to smelters in Russia owned by the plant’s Russian parent company, United Company Rusal.
After processing the alumina into aluminum, the smelters have sold more than $650 million worth of the metal to a Moscow-based trader, Aluminium Sales Company (ASK), which supplies aluminum to clients that include dozens of EU-sanctioned Russian weapons manufacturers, according to leaked transaction data. (The data does not detail the volume of aluminum sold.)
Weapons made by these firms have leveled entire city blocks in Mariupol, struck a children’s hospital in Kyiv, and blown open an apartment building in western Ukraine, according to EU sanctions listings, Ukraine’s military intelligence, and the London-based Royal United Services Institute (RUSI).
Aughinish Alumina’s exports to Russia — which have increased since the full-scale invasion of Ukraine — are entirely legal under EU trade rules. That is because despite the bloc’s recognition of alumina’s importance, no restrictions have been placed on the product’s export to Russia.
The EU banned imports of aluminum produced in Russia in February 2025 in an effort to sever an income stream that could be used to fund Moscow’s war. But it has not prohibited the export of alumina to Russia, despite calls from the Latvian government which argued that a ban would “weaken [Russia’s] war machine.”
When reached for comment, Aughinish told OCCRP that it operates “in strict compliance with all applicable European Union laws, including sanctions, export control measures and trade regulations.” The company said it had implemented “robust sanctions compliance and due diligence framework covering its entire supply chain,” though it did not respond to specific questions about whether its products might be used to build Russian weapons.
The firm emphasized that alumina and aluminum are basic commodities serving “broad general purpose societal needs…vital for countless civilian industries.”
Alex Prezanti, a U.K. barrister and sanctions specialist, said the lack of restrictions on the alumina trade reflects the tightrope the EU must walk as it tries to stem the flow of money and materials to Russia without compromising the bloc’s own economic interests.
“EU policymakers have to draw a balance between potential impact of sanctions on Russia and potential impact of sanctions on their domestic economies,” said Prezanti, a co-founder of the State Capture Accountability Project non-profit.
No further action was taken on alumina “either because the EU didn’t think that it would have sufficient impact, or because one or more member states decided that this ban was not in their national interests.”
The European Commission did not respond to requests to comment.
Ireland’s Department of Foreign Affairs and Trade stressed that alumina is “not a sanctioned good” and “therefore its export to other countries, including Russia, is not restricted.”
A lack of data makes it “difficult to ascertain where Russia is sourcing its tools and weapons from,” a spokesperson said, adding that “Ireland remains unequivocal in its continuing support for Ukraine in light of Russia’s unjustified invasion.”
Oleksandr V. Danylyuk, a former Ukraine defense official who is now a fellow at the think-tank RUSI, sees a concerning contradiction. In his view, supplying Russia with EU-made alumina “could undermine NATO’s stated goals of supporting Ukraine and deterring Russia.”
Pavlo Shkurenko, a Sanctions Research Fellow at Kyiv School of Economics Institute, also warns that Europe’s “entanglement” with Russia’s metallurgical sector carries serious risks for the continent.
It enables “not only direct daily attacks on Ukrainian civilians, but also potential confrontation with Europe itself, as the development of Russian military industry suggests.”
The Russian Ministry of Defense, ASK, and Rusal and its parent company EN+ Group did not respond to OCCRP’s request for comment.
‘A Strategic Asset’
Aughinish Alumina’s Russian parent company, Rusal, is one of the world’s largest aluminum producers, with mines, refineries, and smelters across the globe. In Russia, it is the primary supplier of aluminum for the defense, transport, construction and electrical industries.
After Russia’s 2022 invasion of Ukraine, the EU sanctioned Rusal’s founder and former top shareholder Oleg Deripaska, a billionaire and close ally of Russian President Vladimir Putin, for his alleged involvement in companies working with the Russian defense sector. (Deripaska did not respond to OCCRP’s request for comment, but has mounted failed legal challenges to U.S., EU, and Australian sanctions against him.)
Rusal, however, remained untouched, sparking a debate in the Irish parliament about the company’s plant in County Limerick, which produces around a third of the EU’s alumina.
“We appear to be protecting the Aughinish Alumina plant from sanctions,” then-MP Thomas Pringle said in April 2022. “That is hypocritical of us. If we need to protect that plant, the Government should be considering taking it over straight away and…take it out of the hands of the oligarchs.”
The country’s then minister of state, Patrick O’Donovan, responded by saying that the plant “is not connected…to any sort of Russian empire,” and that it was a major employer and supplier of alumina to European industries.
Rusal itself had actually been briefly sanctioned back in 2018 by the U.S. for its connection to Deripaska. The move sent shockwaves through the global aluminum industry and led to a surge in aluminum prices. Not long after, the U.S. agreed to delist the company after Deripaska reduced his shares in Rusal’s parent company to a minority stake.
Ireland’s former ambassador to the U.S., Daniel Mulhall, told The Irish Times that he lobbied to keep the Aughinish Alumina plant open, as it was “one of the few European strategic assets that we had in Ireland” at the time.
But questions over the refinery were raised again in 2023, when Irish lawmaker Réada Cronin asked why Russia was buying so much alumina from the country, given that “such exports are capable of assisting Russia in its invasion of Ukraine.”
Ireland’s then-trade minister Simon Coveney responded only by saying that the alumina exports were in compliance with EU sanctions.
From Guinea to Siberia
In 2024, for instance, Aughinish sent around half of all its refined alumina produced that year — worth around $400 million — to Krasnoyarsk and Sayanogorsk, accounting for nearly 40% of the alumina imported by the smelters.
That year, the two smelters produced over a third of Rusal’s entire aluminum output, according to annual reports.
But that’s where the public paper trail ends, with Rusal making no public mention of supplying Russian arms manufacturers.
Leaked transaction data, however, allowed reporters to follow the aluminum’s path.
From Russian Smelters to Ukraine’s Frontlines
The leaked transaction data obtained by reporters shows ASK paid Rusal’s trading arm more than $640 million for aluminum from the company’s smelters between the start of the full-scale invasion in February 2022 to April 2025.
(While the data does not show the exact volumes ASK sourced from each smelter, it shows the trader also paid service fees to specific smelters for loading and unloading aluminum, some 40 percent of which went to Krasnoyarsk and Sayanogorsk.)
Throughout the same time period ASK, in turn, made approximately a third of its revenue — some $337 million — selling aluminum for the purpose of Russian defense contracts.
Reporters were unable to trace alumina from Aughinish to a specific product. However, ASK’s 2024 customer list included more than 40 EU-sanctioned companies — many owned by the Russian defense conglomerate Rostec — which produce weapons including anti-aircraft missiles, rocket systems, and long-range bombers, according to sanctions listings.
Eighteen of these companies have built arms directly used in deadly attacks in Ukraine, said Andriy Yusov, an official from the Main Directorate of Intelligence of the Ministry of Defense of Ukraine, which analyzes the debris of Russian weaponry found on Ukraine’s battlefields.
One of the trader’s biggest customers is Kamaz, a manufacturer of heavy-duty vehicles used by Russia’s armed forces in Ukraine, according to its EU sanctions listing. In 2024, Kamaz paid ASK $16 million for aluminum, the data shows.
Another top ASK client is the U.S.- and EU-sanctioned Votkinsk Machine Building Plant, which bought $101,200 worth of aluminum from ASK in 2024.
According to EU authorities and Ukraine’s military intelligence agency, the Votkinsk plant manufactures a range of armaments, including long-range missiles and the short-range Iskander ballistic missile — a weapon that reportedly killed 31 civilians in an attack in the northeastern city of Sumy in April 2025.
Kamaz, Votkinsk, and eleven other sanctioned arms manufacturers that buy aluminum from ASK did not respond to requests to comment.
NATO and EU leaders have issued repeated warnings regarding the strategic threat posed by systems developed by Russia’s arms manufacturers.
“Putin’s war machine is speeding up – not slowing down,” NATO Secretary General Mark Rutte said last summer in a speech that highlighted Russia’s growing weapons production.
“Let’s not kid ourselves; we are all on the eastern flank now,” he warned. “The new generation of Russian missiles travel at many times the speed of sound.”
Khadija Sharife, Alina Tsogoeva (OCCRP), Kaur Maran (Eesti Ekspress), Simon Goodley (The Guardian), Maksym Dudchenko (KibOrg), and Lars Bové (De Tijd) contributed reporting.
-

Unlearning the Myth of Red Texas
In Texas, our heritage is a sacred cow. We close our eyes and we can see the huge sky, the mesquite trees in the hill country, the spindly pines in the east, where I am from, and the green waters of Galveston. We watch Westerns—my father loves them—and we see ourselves in the outlaws, the cowboys who rode across the open range with their cattle, bandanas pulled over their noses to keep out the dust. Though I am from the suburbs, a creature of air conditioning far removed from any kind of cowboy living, I spent nearly every weekend for a decade in a more rural corner of Harris County, riding horses behind a limestone house. There was perhaps nothing I heard more during my lessons than, “Get tough!” And as I did, a small child alone atop a horse kicking him along with all of my might, I had a latent sense that I was participating in some grand tradition. Under that sticky, humid, unrelenting Texas sun, you whip the horse, you do the work, and for the love of all things good, you do not talk back (which of course, I was liable to do, anyways). This was what we got for being born in Texas: an inheritance of grit, land and rugged individualism that our state has proudly fought for since its inception. Hell, even our zip-loc bags, purchased from beloved local grocery chain H-E-B, read “Texas Tough.”

-
Six Stand Trial in France as Marseille’s Deadly Drug War Enters the Courtroom
The trial of six men accused of being key figures in the notorious “DZ Mafia” opened on Monday in southern France, pulling back the curtain on a ruthless organized crime syndicate that has fueled a bloody drug war across the Mediterranean port city of Marseille.
“The Court of Appeals in Aix-en-Provence regularly hears high-profile cases involving organized crime, but this is the first major case involving the key figures of the DZ Mafia,” Baptiste Barles, the court’s communications director, told OCCRP.
Appearing before the Assize Court of Aix-en-Provence, the defendants face charges stemming from a 2019 double murder that authorities say was a calculated underworld hit. The proceedings, expected to last three weeks, mark a significant moment in France’s ongoing battle against a wave of hyper-violent narcotics gangs.
The case centers on the brazen killings of Farid Tir, 29, and Mohamed Bendjaghlouli, who were found with fatal gunshot wounds in a hotel room on Aug. 30, 2019. Investigators maintain that Mr. Tir, a prominent figure in Marseille’s illicit drug trade, was the primary target of the assassination.
Among the six men currently standing trial are Amine Oualane and Gabriel Ory, who prosecutors allege are the current leaders of the DZ Mafia. The syndicate, whose name is a nod to the alpha-2 country code for Algeria—highlighting the origins of its founding members—was born in the housing projects of Marseille but has since metastasized, expanding its operations to several cities across France.
The syndicate’s violence has sparked a broader judicial reckoning. Next fall, the same court will hear another trial tied to the DZ Mafia: the murder of a brother of Amine Kessaci, a political and civil society activist involved in the fight against drug trafficking in Marseille.
Authorities accuse the group of orchestrating a sprawling criminal enterprise that includes drug trafficking, kidnapping, and contract killings.
The Rise of “Narchomicides”
The trial unfolds against the backdrop of a grinding turf war in Marseille, where rival factions are fighting violently for control of lucrative drug-selling territories. The bloodshed has become so pervasive, and the collateral damage so high, that Dominique Laurens, the city’s former public prosecutor, coined a new term for the crisis: “narchomicides,” or murders directly tied to the drug trade.
In response to the escalating violence, the French state has recently intensified its crackdown on the syndicate’s infrastructure.
In early March, a sweeping police action dubbed Operation “Octopus” led to the arrest of 43 individuals suspected of playing significant roles within the DZ Mafia. During the raids, authorities seized assets valued at more than 4 million euros (about $4.6 million).
Broader investigations have also exposed the group’s deep financial networks. A recent cross-border money laundering probe uncovered the syndicate’s international reach, resulting in the seizure of over 40 million euros ($46.3 million) across France and Italy.
The French Gendarmerie, which mobilized heavily for the recent raids, indicated that the state is changing its approach to dismantling these cartels.
“This crackdown illustrates the gendarmerie’s shift in strategy in the fight against these structured criminal networks embedded at the heart of society,” the agency said in a statement.
-
Join Internet Archive and Partners for the National Summit on Local News Preservation
Join Internet Archive, Investigative Reporters and Editors (IRE), and the Poynter Institute for the National Summit on Local News Preservation. This event will bring together the producers, preservers, and users of local news to develop collaborative, scalable solutions to address the urgent preservation challenges presented by the rapidly changing local news landscape.
This free, in-person event will be held on June 17, 2026 in conjunction with the IRE 2026 Conference in National Harbor, Maryland just outside of Washington, DC.
Through panels, presentations, and facilitated discussions, Summit attendees will:
- Discover proven strategies and partnerships behind successful local news preservation initiatives
- Shape recommendations for local news preservation to be distributed nationally to newsrooms and memory institutions
- Network with leaders from news and cultural heritage organizations
- Explore tools and programs that can support the preservation and access of local digital news assets
Learn more and register to attend!
This event is part of Today’s News for Tomorrow, a program supported by Press Forward. Additional support for the Summit has been provided by the Society of American Archivists Foundation.
-
Romanian Tycoon Linked to Sanctioned Belarusian Elites and Russian Drone Makers
Romanian businessman Vitalie Buzdugan has quietly built a sprawling network of at least 15 companies in Belarus, deeply intertwining his financial interests with politically connected figures in the inner circle of President Alexander Lukashenko, according to a new investigation by the independent outlet Buro Media.
The article reveals that Buzdugan holds major stakes across a broad swath of the Belarusian economy, including the medical, cultural, construction, technology, tourism, and agricultural sectors.
Many of these enterprises are tied, directly or indirectly, to Alexander Zaytsev, a prominent businessman heavily sanctioned by both the European Union and the United States. The network also links back to Igor Rachkovsky, the former chief of the Belarusian border service and reportedly a longtime friend of Lukashenko’s eldest son, Viktor.
Property records reviewed by journalists indicate that Buzdugan’s wealth extends to prime real estate in Minsk. This includes three apartments on Tikhaya Street, an upscale neighborhood situated near areas favored by the Belarusian elite.
Expansion in the ‘Great Stone’
One of the clearest examples of Buzdugan’s expanding footprint is his aggressive move into the Great Stone Industrial Park, a massive special economic zone that offers lucrative tax breaks and regulatory benefits to its residents.
According to the investigation, Buzdugan’s presence in the park surged following a key personnel shift in 2020. That year, Denis Silchenko—identified by Buro Media as a former employee of several Buzdugan companies and the son-in-law of Rachkovsky—assumed a senior role at the park’s development company.
Today, nine of Buzdugan’s companies are registered within Great Stone, despite the fact that only a few appear to align with the industrial park’s stated high-tech profile.
The Russian Drone Connection
The investigation also sheds light on Plasma Union, a company established in 2023 to manufacture blood plasma medicines.
A letter obtained by Buro Media includes excerpts from the minutes of a December 2023 Health Ministry meeting regarding Plasma Union’s offer to invest $10 million in a manufacturing plant in the Belarusian town of Gantsevichi. Furthermore, the minutes reveal that the company was preparing to construct a second facility inside the Great Stone park. The document explicitly noted that “partners from the Russian Federation” would export the entirety of the plant’s output.
Those Russian partners include Alexey Ordzhonikidze, a co-owner of Plasma Union. Buro Media linked him to a prominent Russian family, noting that the investigative outlet IStories previously revealed Ordzhonikidze held a stake in the company that produces the strike drones currently used by the Russian military in its war against Ukraine.
Reached by phone for comment on the investigation, Buzdugan denied any involvement in the businesses and stated he had never engaged in joint projects with Zaytsev. He declined to answer any further questions.
-
‘CanisterWorm’ Springs Wiper Attack Targeting Iran
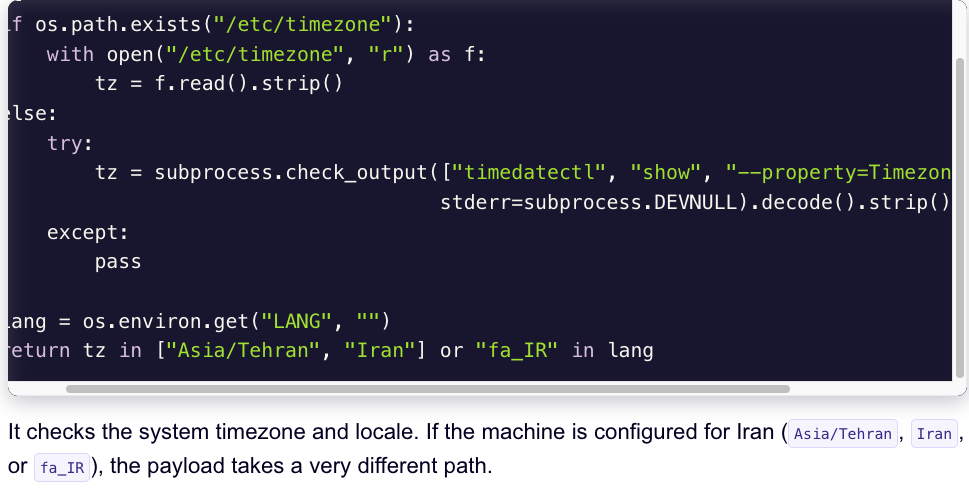
A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have Farsi set as the default language.
Experts say the wiper campaign against Iran materialized this past weekend and came from a relatively new cybercrime group known as TeamPCP. In December 2025, the group began compromising corporate cloud environments using a self-propagating worm that went after exposed Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. TeamPCP then attempted to move laterally through victim networks, siphoning authentication credentials and extorting victims over Telegram.
A snippet of the malicious CanisterWorm that seeks out and destroys data on systems that match Iran’s timezone or have Farsi as the default language. Image: Aikido.dev.
In a profile of TeamPCP published in January, the security firm Flare said the group weaponizes exposed control planes rather than exploiting endpoints, predominantly targeting cloud infrastructure over end-user devices, with Azure (61%) and AWS (36%) accounting for 97% of compromised servers.
“TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques,” Flare’s Assaf Morag wrote. “The group industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem.”
On March 19, TeamPCP executed a supply chain attack against the vulnerability scanner Trivy from Aqua Security, injecting credential-stealing malware into official releases on GitHub actions. Aqua Security said it has since removed the harmful files, but the security firm Wiz notes the attackers were able to publish malicious versions that snarfed SSH keys, cloud credentials, Kubernetes tokens and cryptocurrency wallets from users.
Over the weekend, the same technical infrastructure TeamPCP used in the Trivy attack was leveraged to deploy a new malicious payload which executes a wiper attack if the user’s timezone and locale are determined to correspond to Iran, said Charlie Eriksen, a security researcher at Aikido. In a blog post published on Sunday, Eriksen said if the wiper component detects that the victim is in Iran and has access to a Kubernetes cluster, it will destroy data on every node in that cluster.
“If it doesn’t it will just wipe the local machine,” Eriksen told KrebsOnSecurity.
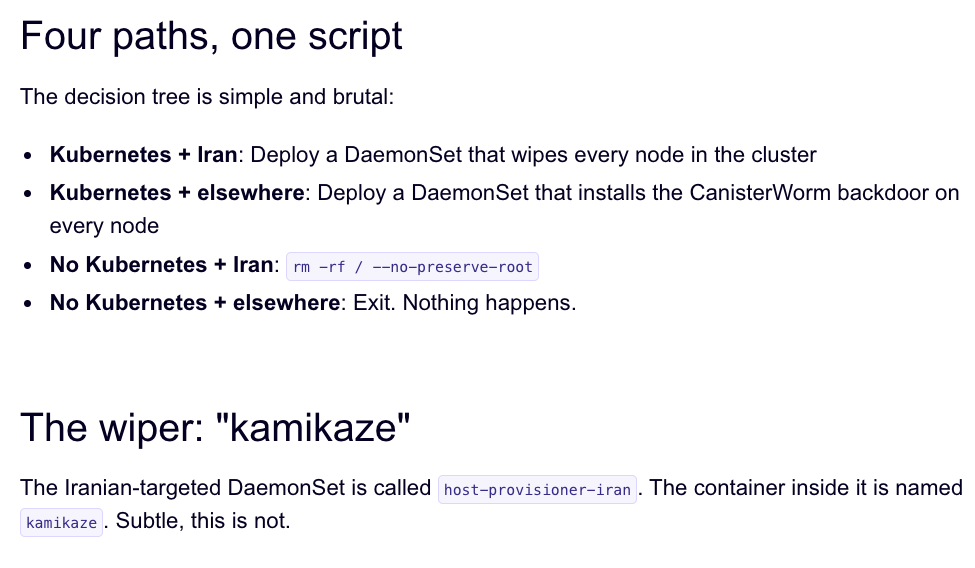
Image: Aikido.dev.
Aikido refers to TeamPCP’s infrastructure as “CanisterWorm” because the group orchestrates their campaigns using an Internet Computer Protocol (ICP) canister — a system of tamperproof, blockchain-based “smart contracts” that combine both code and data. ICP canisters can serve Web content directly to visitors, and their distributed architecture makes them resistant to takedown attempts. These canisters will remain reachable so long as their operators continue to pay virtual currency fees to keep them online.
Eriksen said the people behind TeamPCP are bragging about their exploits in a group on Telegram and claim to have used the worm to steal vast amounts of sensitive data from major companies, including a large multinational pharmaceutical firm.
“When they compromised Aqua a second time, they took a lot of GitHub accounts and started spamming these with junk messages,” Eriksen said. “It was almost like they were just showing off how much access they had. Clearly, they have an entire stash of these credentials, and what we’ve seen so far is probably a small sample of what they have.”
Security experts say the spammed GitHub messages could be a way for TeamPCP to ensure that any code packages tainted with their malware will remain prominent in GitHub searches. In a newsletter published today titled GitHub is Starting to Have a Real Malware Problem, Risky Business reporter Catalin Cimpanu writes that attackers often are seen pushing meaningless commits to their repos or using online services that sell GitHub stars and “likes” to keep malicious packages at the top of the GitHub search page.
This weekend’s outbreak is the second major supply chain attack involving Trivy in as many months. At the end of February, Trivy was hit as part of an automated threat called HackerBot-Claw, which mass exploited misconfigured workflows in GitHub Actions to steal authentication tokens.
Eriksen said it appears TeamPCP used access gained in the first attack on Aqua Security to perpetrate this weekend’s mischief. But he said there is no reliable way to tell whether TeamPCP’s wiper actually succeeded in trashing any data from victim systems, and that the malicious payload was only active for a short time over the weekend.
“They’ve been taking [the malicious code] up and down, rapidly changing it adding new features,” Eriksen said, noting that when the malicious canister wasn’t serving up malware downloads it was pointing visitors to a Rick Roll video on YouTube.
“It’s a little all over the place, and there’s a chance this whole Iran thing is just their way of getting attention,” Eriksen said. “I feel like these people are really playing this Chaotic Evil role here.”
Cimpanu observed that supply chain attacks have increased in frequency of late as threat actors begin to grasp just how efficient they can be, and his post documents an alarming number of these incidents since 2024.
“While security firms appear to be doing a good job spotting this, we’re also gonna need GitHub’s security team to step up,” Cimpanu wrote. “Unfortunately, on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix.”
-
Poisoned Trekkers and Phantom Flights: Nepal Charges 32 in Massive Himalayan Rescue Scam
For years, the towering peaks of the Himalayas have drawn thousands of thrill-seekers to Nepal. But according to prosecutors, many of those tourists were led into a carefully orchestrated trap: secretly fed baking soda by their own guides to induce severe illness, only to be “rescued” in a highly lucrative insurance fraud scheme.
Following a sprawling, months-long police investigation, authorities filed organized crime and fraud charges against 32 individuals in the Kathmandu District Court. The case implicates a deep network of prominent tourism stakeholders, including trekking agency owners, helicopter operators, and hospital executives.
Nine suspects were produced in court on Sunday, while 23 others remain at large.
The Mechanics of the Fraud
The charges detail a brazen exploitation of the very systems designed to keep mountaineers safe. According to investigators, trekking agencies intentionally made their clients sick, often by lacing their food with baking soda, which can cause severe gastrointestinal distress mimicking altitude sickness or food poisoning.
Once trekkers were incapacitated, the agencies forced them to agree to emergency helicopter evacuations. The operators then produced forged medical and flight documents to bill international travel insurance companies for the exorbitant costs of the phantom emergencies.
The illicit profits were subsequently divided among the guides, the helicopter companies, the trekking agencies, and the cooperating hospitals where the tourists were supposedly treated.
“A charge sheet has been filed at the court,” said Dipak Kumar Shrestha, a spokesperson for the Kathmandu District Court. “The court is recording statements of the accused, giving high priority to this high-profile corruption case.”
In January, authorities arrested six executives from three prominent mountain rescue agencies. Police said that the agencies not only forced unnecessary evacuations but systematically fabricated the paperwork required to pocket the emergency funds.
A Multimillion-Dollar Syndicate
Prosecutors are seeking a staggering 1.51 billion Nepalese rupees (ca. $11.3 million) in total fines from the accused, with penalties varying based on individual offenses.
According to police records, the group scammed at least $19.69 million in insurance money. The investigation accused the Mountain Rescue Service P.Ltd. of orchestrating 171 “suspicious rescues” out of the 1,248 it arranged, netting an estimated $10.3 million in collaboration with local hospitals.
The Nepal Charter Service P. Ltd. is accused of syphoning approximately $8.2 million while the Everest Experience and Assistance P.Ltd. is believed to have scammed about $1.1 million.
A Long-Buried Scandal Revived
The fraudulent rescues have long been an open secret in Kathmandu, severely damaging Nepal’s reputation in the global adventure tourism market. In recent years, several major international insurers, including Travellers Assists, completely stopped selling coverage for tourists trekking in Nepal due to the rampant fraud.
Following international media reports in 2018, the Nepalese government formed a probe panel comprised of tourism bureaucrats to investigate the claims. However, the panel’s findings were never made public, and the implicated companies faced no disciplinary action.