The Israeli Air Force (IAF) has dropped 5,000 bombs on Iran since the United States and Israel launched an attack last week, according to a statement by the IAF on March 4.
Bellingcat has monitored weapons used in the first few days of the war, and strikes across the region, including those that caused civilian harm. Some weapons, such as the US Precision Strike Missile, have seen their first use in combat. A variant of the Tomahawk missile, previously unknown to the public, was also used.
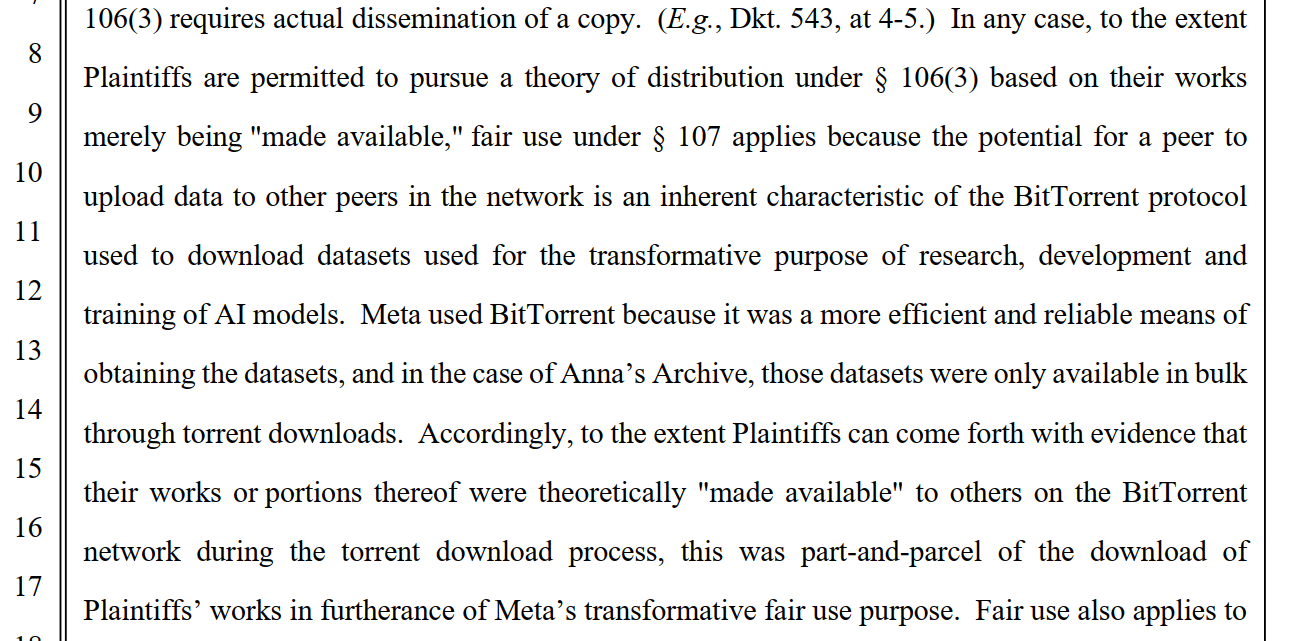
On March 3, the IAF posted three images in three separate posts showing a bomb not publicly seen in Israeli service before. The Israel Air Force released these photos accompanied with claims they were of jets participating in the strikes on Iran. Experts told Bellingcat that this bomb appears to have an incendiary component, and may be one intended to destroy chemical or biological warfare agents.
The images appear to show 2,000-pound-class air-delivered bombs fitted with Joint Direct Attack Munition (JDAM) guidance kit with a red band around the nose. Red is commonly used to denote an incendiary, while yellow indicates high explosive effect.

We identified key details about the munition and shared the images with two weapons experts.
Apparent Similarities to the MK 84
Dr N.R. Jenzen-Jones, the director of Armament Research Services (ARES), a weapons intelligence consulting company, told Bellingcat these images show a 2,000-pound-class air-delivered bomb fitted with a Joint Direct Attack Munition (JDAM) guidance kit.
Frederic Gras, an Explosive Remnants of War (ERW) expert, also told Bellingcat that the bomb could be of the US MK 80 series, or an Israeli copy, and has a JDAM guidance kit.

The US JDAM bomb guidance kit is designed for use with bombs that use the MK 80 series bomb bodies, and the closely related BLU-109 “bunker buster” body.
The Open Source Munitions Portal added the munition to their website on March 3, describing it as “visually similar to a MK 84 general purpose aerial bomb”, while noting that “the marking scheme is distinctly different”. The War Zone also reported on these distinct markings, and possible munitions it could be.

“The combination of yellow and red bands probably indicates both a high explosive and incendiary payload, which would be consistent with a 2,000-pound-class bomb of MK 84 form factor known as the BLU-119/B Crash Prompt Agent Defeat (CrashPAD),” Dr Jenzen-Jones told Bellingcat.
Frederic Gras, an Explosive Remnants of War (ERW) expert said that the US and Israel both use red markings to indicate an incendiary payload, or effect. The bomb could be a full incendiary payload, with the yellow band indicating a bursting charge, or it could be a bomb primarily with a high explosive component, and a secondary incendiary effect, Gras added.
Red Bands on Israeli Weapons
It’s not the first time the Israeli Air Forces has published weapon images with red bands marking the warhead or payload section of a munition. Shortly after the start of the Gaza War in 2023, the IAF posted a photo which included an Apache attack helicopter with a Hellfire missile with a red band. The IAF deleted the post and replaced it with a similar photo of an Apache without this missile.

This fueled speculation online that this could be an incendiary or the thermobaric variant of the Hellfire missile, the AGM-114N. It has been approved by the US for sale to Israel.
M825A1 155mm white phosphorus artillery projectiles, munitions designed to create smoke, used by Israel also have a red band and a yellow band around the nose.
Israeli munitions which are not incendiary have also been spotted with light red bands over the fuel tanks for munitions with jet engines, such as the Delilah cruise missile.

Designed To Target Chemical or Biological Weapon Stockpiles
The markings are consistent with the US-produced CrashPAD, but “given the possible CBW [chemical and biological warfare] threats Israel has long faced from Iran, it is entirely plausible that an Israeli analogue was developed,” Dr Jenzen-Jones told Bellingcat.
The CrashPAD contains white phosphorus and high explosives, and is designed to destroy biological and chemical warfare agents according to US government documents.

Dr Jenzen-Jones told Bellingcat that the CrashPAD is the only publicly known weapon of this type utilising a MK 84 bomb body although there are several programs producing similar munitions. A penetrating variant is known as the Shredder but it uses a modified BLU-109 bomb body, which is visually different from the MK 84 bomb body visible in the IAF photos.

CrashPAD has been in the US inventory for nearly two decades. “Chemical Agent Defeat weapons, such as Crashpad, are not illegal”, and they must undergo a legal review to ensure compliance with US domestic and international law, Michael Meier, former Senior Advisor to the Army Judge Advocate General for Law of War and current Adjunct Professor at Georgetown University Law Center, told Bellingcat.
“The express purpose for the reservation is that these weapons, such as Crashpad, are the only weapons that can effectively destroy certain targets such as biological weapons facilities, for which high heat would be required to eliminate bio-toxins,” Meier said.
Dr Arthur van Coller, Professor of International Humanitarian Law at the STADIO Higher Education, told Bellingcat that “if the CrashPAD is used as designed, i.e. to target chemical or biological weapon stockpiles sufficiently removed from civilian populations, then its use is consistent with IHL [International Humanitarian Law] and treaty law, even under CCW [Certain Conventional Weapons], Protocol III.”
Dr Arthur van Coller also said that the “United States and Israel are State Parties to the CCW itself,” but only the US is also a party to Protocol III on incendiary weapons, albeit with reservations, which means that Israel “is not legally bound by Protocol III’s restrictions on incendiary weapons (including those applying to CrashPAD) under treaty law”. Iran is not a party to the CCW at all.
The US is a major supplier of weapons to Israel, and has sent thousands of MK 80 series and BLU-109 bombs to the country. Israel also produces some MK 80 series bombs.
Israel and US Responses
The US Defense Security Cooperation Agency, which publishes details of some major arms sales, does not mention any transfers of the CrashPAD. Bellingcat asked the Department of State if the CrashPAD or weapons with similar capabilities were transferred to Israel. Bellingcat also asked the Department of State if they assessed that Iran had a chemical weapons program. A State Department Spokesperson told Bellingcat that “The Trump administration backs Israel’s right to self-defense” and referred Bellingcat to the IDF for questions about procurement and munitions used.
The US Department of Defense did not respond to requests for comment by the time of publication.
Bellingcat asked the IDF what the bomb was, if it was supplied by the US, if it contained white phosphorus, thermobaric or fuel air explosives, and if the IDF assessed that Iran had a chemical weapons program. The IDF told Bellingcat that it “will not be able to provide details regarding the types of munitions it uses. With that said the IDF uses only legal weapons and ammunition.”
Bellingcat’s Carlos Gonzales contributed research to this article. Livio Spaini from Bellingcat’s Volunteer Community also contributed to this piece.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here, Instagram here, Reddit here and YouTube here.
The post The Incendiary Bomb Never Seen in Israel Before appeared first on bellingcat.